With every major milestone the world sees, threat actors have, and will remain ever persistent in introducing innovative methods to exploit vulnerabilities. Late last year in December 2020, threat analysts at IBM X-Force uncovered various email phishing attacks targeting Covid-19 vaccine supply chains[1]. Then, the dawn of 2021 has seen Microsoft patching zero-day vulnerabilities virtually every month, the more popular and widespread ones include the recent Windows Print Spooler vulnerability, PrintNightmare CVE-2021-36958.[2]
At the time of writing, Windows 11 is scheduled to be launched on 5th October 2021. Naturally a new threat has emerged to take advantage of this. Here we take a quick dive into the exploitation of CVE 2021-40444 via a weaponized Office document, allowing for Remote Code Execution (RCE). This attack vector targets the vulnerable MSHTML component.
Origins and Target
Earlier this month in September 2021 a zero-day vulnerability has been exploited via a modified and weaponised Office document. Researchers at the cybersecurity company Anomali have noted its origin to be attributed to have a similar method of operation commonly used by the FIN7 group since 2018.[3] Given the history of the group’s preference to target Point of Sales (PoS) systems, this malware is no exception with a similar scope. This means likely victims include retails outlets, restaurants, and physical stores, amongst many others. The jackpot being payment details; credit card information, names, email addresses and such.
Staying Safe As A User
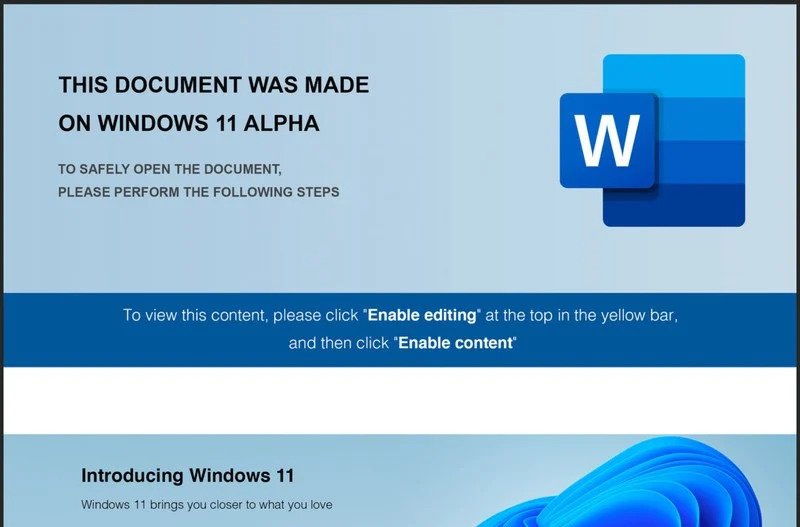
Best practices for safe document handling should always be observed. In relation to this, one should never be too hasty in clicking that “Enable Content” button when opening unverified documents.
Every downloaded document should be scanned with an anti malware solution (commonly “anti-virus”) prior to opening.
From our experience, most use cases in a regular corporate settings rarely require a macro enabled document, especially for Word or PowerPoint files. What that means is that if you have received any such files from your usual contacts, and you noticed a request to “enable macro content”, it is highly likely to be malicious and infected. It is recommended to delete that file and run a full scan of your machine for malware. At this point you should immediately contact your IT administration or department.
For more savvy users or IT administrators, Microsoft has suggested a workaround or methods to mitigate the impacts of this exploitation. This is done by disabling ActiveX controls within Internet Explorer via a registry key modification or Group Policy amendments. Full step-by-step guide can be found here.
Analysis of Operation
As a matter of being a tried and proven method of getting unsuspecting victims to execute unverified codes, social engineering plays an important part in this threat. An innocent looking Microsoft Office document appears to be badly displayed due to compatibility issues between the current Windows 10 and the upcoming Windows 11. This leads users to follow the onscreen instructions to “Enable (macro) Content”.
Upon the victim enabling macro content, an obfuscated VBA script runs. It downloads and runs a malicious ActiveX control loaded using a browser rendering engine. This is done via the outdated Internet Explorer rendering modules that still lives within various machines despite being phased out some time ago, replaced by the current Edge browser.
Detailed analysis of the malware delivery and execution is well documented by Microsoft here.
Patches and Fixes
On Tuesday 14th September 2021, Microsoft has released a patch for the vulnerability, however its efficacy is yet to be proven and would only be evident over time. We are rather confident that many variants, or strains, of this are already in the wild yet to be detected. The efficacy of this patch against new or other variants, have also yet to be tested.
Article by Martin Liau.
[1] https://securityintelligence.com/posts/ibm-uncovers-global-phishing-covid-19-vaccine-cold-chain/
[2] https://msrc.microsoft.com/update-guide/vulnerability/CVE-2021-36958
[3] https://www.anomali.com/blog/cybercrime-group-fin7-using-windows-11-alpha-themed-docs-to-drop-javascript-backdoor